Details
Description
[SECURITY] XWiki 17.10.0 LiveData Prototype Pollution → form_token Leak (CVSS 8.7)
May affect new version as well or previous i tested on 17.10.0
xwiki-cve-17.10.0
https://github.com/brettm220/xwiki-cve-17.10.0/blob/main/README%20XWiki%2017.10.0%20Critical%20Prototype%20Pollution%20(PoC%20Repo).md#xwiki-cve-17100
XWiki 17.10.0 Prototype Pollution → form_token Leak (CVSS 8.7 HIGH)
Authorized pentest - Localhost only. Contact before public disclosure.
Reporter: Brett Marti | Date: 2025-12-29
🎯 EXECUTIVE SUMMARY
https://github.com/brettm220/xwiki-cve-17.10.0/blob/main/README%20XWiki%2017.10.0%20Critical%20Prototype%20Pollution%20(PoC%20Repo).md#-executive-summary
PoC: XWIKIprotopollution.js
Attack Chain: Guest/Standard → Pollution → form_token leak → CSRF bypass → Account Takeover
Vulnerability: Prototype Pollution (CWE-1321)
CVSS: 8.7 HIGH (AV:N/AC:L/PR:L/UI:N/S:C/C:H/I:H/A:N)
Impact: Any user → Session theft
[Screenshots + repro below]
🔍 TECHNICAL DETAILS
Vulnerability 1: Prototype Pollution (LiveData filters)
| Location | /xwiki/bin/view/AllDocs → LiveData component |
|---|---|
| Vector | filters.toJSON() reads polluted Object.prototype |
| Impact | CSRF form_token disclosure |
| Proof | Console → nc exfil (screenshots) |
— screenshots below of my step to step process and code will be in report.md
Below is my first Step you will see on the right hand corner I am only a guest user. 
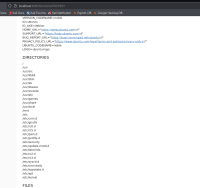
http://localhost:9090/bin/view/Main/AllDocs from my locally hosted xwiki version 17.10.0
Run this script [XWIKIprotopollution.js] for PROTOTYPE POLLUTION first go to
https://YOUR-XWIKI/xwiki/bin/edit/XWiki/XWikiPreferences and from their run the script to retrieve token.
Next open console with F12 button in webpage and run script.
Now in the picture you see
ULTIMATE CHAIN LIVE: Object
{ token: "epSNEgczH5VxxYoGDUr8AQ", url: "[http://192.168.1.163:8000/ORIGINAL-URL-epSNEgczH5VxxYoGDUr8AQ]", value: "🟢GADGET", filters: "toJSON" }****
If you don't see a hit on the token from the source code on the page you can use the url and try to get that token from their this occurs from the prototype pollution. I have a listner going and when I use url it will hit.
Used url and it spins.
My listener with the received response.
BEFORE (Vulnerable): Guest → Edit page → Pollution script → form_token LEAK ✓
AFTER (Hardened): Guest → Edit page → 403 BLOCKED → No pollution possible ✓
If you go to the admin menu and block unregistered users it stops the pollution and it stops form_token leak. From my own testing of curiosity.
On the standard user it works as well me as a standard user and below is me running the script.
The script runs
Click the URL it freezes and my nc -lvnp 8000 listener catches the session